S1REN's Zero to Navy Seal of Crackin'


Good Luck, Intruder.
Hey, this is S1REN's totally NON-generic step-by-step process to get from zero to Navy Seal of crackin'
========================================================================================
PT 1
1. Install Kali Linux:
https://www.kali.org/get-kali/#kali-platforms
2. Get VirtualBox installed:
https://download.virtualbox.org/virtualbox/7.0.12/virtualbox-7.0_7.0.12-159484~Debian~bookworm_amd64.deb
3. Find an "Easy" machine to hack in preparation for your OSCP from VulnHub. THERE ARE TONS! (I personally have a few hundred under my belt if you need a measure - we did say Navy Seal of crackin' after all).
4. DOWNLOAD the image, put it in a directory called "VMs" on your Kali Machine.
5. INSTALL/IMPORT THE IMAGE, should be as simple as an import. Set your network interface to "bridged" - WARNING - YOU ARE DOING SERIOUS LEARNING HERE AND THIS MEANS YOU WILL BE VULNERABLE IF THE NETWORK IS BRIDGED. However, it's how I learned, so… ¯\_(ツ)_/¯
6. Launch the machine. Get the IP Address of it.
$ ifconfig (determine your private ip address DHCP designation - scan to discover based upon that)
# Oh, my private IP is 192.168.1.36? Gotcha 8)
$ nmap -sn 192.168.1.0-254 (Class-C 192 Private IP-address space SYN-SCAN Host Discovery)
7. EXAMPLE - If the vulnerable machine you downloaded has the name of "HackThisNerd!-v1.0" - then perform a Google search (especially if you're new to OSCP prep) with the query or "dork" of: "HackThisNerd!-v1.0 walkthrough write-up blog"
8. READ the walkthrough, follow each step until you get root!
9. If you learned ANYTHING NEW AT ALL - put that in a flat file on your Kali Linux file system. i.e. I just learned about how to login to MySQL remotely by utilizing the "-h" flag from this machine. Therefor, if the service is called "mysql" - create the file with the filename of "mysqlref" - short for "mysql reference". All together, it should be in your home directory:
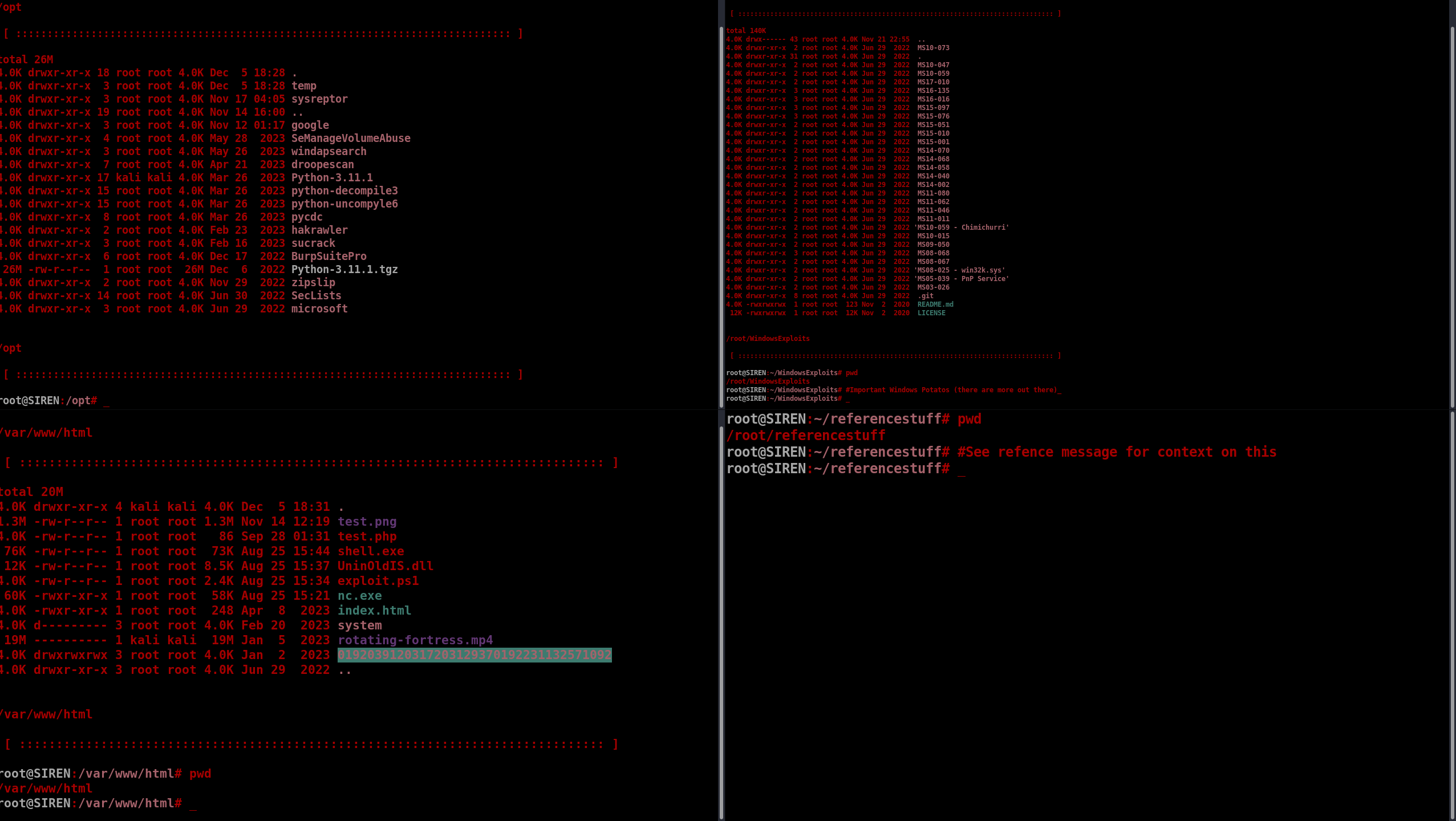
$HOME/referencestuff/mysqlref
10. Switch to Bash as your primary shell.
$ apt-get install -y kali-tweaks
$ kali-tweaks
a. <Set the default login shell to be Bash>
b. <Set the number of lines to by "one-line".
c. Apply the settings from kali-tweaks.
d. Logout.
e. Login.
f. Open a new terminal.
$ echo $SHELL
(should say /bin/bash) - GOOD.
(You now have a .bashrc file. It's a great friend to have.)
11. We're going to take great advantage of that .bashrc file so we never have to leave the terminal ever again for reference when trying to hack a computer/machine during a pentest or learning.
$ nano $HOME/.bashrc
# Scroll to the VERY BOTTOM and add the following bash alias.
alias mysqlref = "clear ; cat $HOME/referencestuff/mysqlref"
12. #RELOAD THE SOURCE:
$ source ~/.bashrc
13. Now, you cracked a machine, you learned something new, you don't want to forget that during an engagement or CTF competition. Therefor, you have bash aliases `cat` the file that corresponds either to the port number, running service, or even an entire topic (such as Active Directory).
14. However, we're working with MySQL as a reference here - so the idea is that anything you learn from these walkthroughs you localize - every single SHRED of information - not a SINGLE thing lost or missed. GET IT ALL!
15. "Okay S1REN, I did all of that and cracked my first machine and have my notation in this flat-file note system you have described. How do I make myself not a n00b or script k1dd1e and be a Navy Seal of Crackin'?"
16. Download 400 more machines and REPEAT the steps for NOTE TAKING and access (on the fly and deployable at any time - even without internet access).
17. This process may take some time. You may learn a lot. Tears may be had. In-fact they will probably be had. Keep adding each of these hacks to your "Arsenal" of techniques.
18. Oh, and on top of all that - use my template to help guide you through a single-target machine and STORE THE NOTES IN CHERRYTREE OR OBSIDIAN. I prefer CherryTree because I like prettier things.
A. QUICK NOTE TAKING HOTKEYS:
Right Click > Paste as plain text (ALWAYS)
B. Highlighting important or low-hanging fruit:
Background Color (BLACK): SHIFT +ALT +B
Foreground Text Color (RED): SHIFT +ALT + F
C. Use the cntrl, shift, and the arrow keys to both move quickly, efficiently, and to select text or entire lines.
Highlight all left: FN + SHIFT + <
Highlight all right: FN + SHIFT + >
Move over words/strings left and right:
Cntrl + Left Arrow
Cntrl + Right Arrow
Beginning and end of lines:
fn + Left Arrow
fn + Right Arrow
^This will take some time and practice - but it's the quickest way to copy, paste, and format notes for important items to stand out quickly. Afterall - we got other machines to get to and we're being timed.
19. USE TERMINATOR!
$ apt-get install -y terminator
# In Kali - go to Settings > Keyboard > "View and Customize Shortcuts"
# Scroll down to "Custom Shortcut"
# Give it a name.
# Set the command to: terminator
# Set the hotkeys to something ergonomically accetable like cntrl + alt + s (should make a triangle)
20. Open Terminator with the new hotkey assigned to it: cntrl + alt + s
Split Vertical: cntrl + shift + e
Split Horizontal: cntrl + shift + o
21. Adjust the colors however you want…
a. Right click > Preferences > ADJUST SETTINGS
b. Right Click > Preferences > Profiles > Scrolling
--> SET THIS TO:
# Scrollbar is "on the right side"
# UNCHECK "Scroll on output"
# CHECK "Scroll on Keystroke"
# CHECK "Infinite Scroll back"
c. Right Click > Preferences > Background
# SET TO SOLID COLOR FOR BEST VISIBILITY.
D. Set your colors however you want.
F. Remove scrollbars, menu bars, set cursor to "Underscore", blinking, and flash a color instead of a sound. Mine looks like this:
=========================================================================================
PT 2.
1. Use my Common - it will help you a lot.
https://sirensecurity.io/blog/common/
Use my Linux Privilege Escalation Guide:
Linux Privilege Escalation - Resources
Use my Windows Privilege Escalation Guide (learn AV Bypass Seperately):
Windows Privilege Escalation - Resources
2. ALMOST ALL of the shells you get will come from the web surface, this will result in no TTY
(read up on PSEDUO TELETYPE DEVICE HISTORY).
Break Out. Get that tty.
a. These are commands you can keep in $HOME/referencestuff/common
b. echo "alias common='clear ; cat $HOME/referencestuff/common'" >> $HOME/.bashrc
c. If that command doesn't work, it's because of "pretty ASCII characters" - just type it out.
You will now have a stable, fully colorized, human-readable, and a valid TTY shell (similar to SSH) that WILL NOT DROP if you ever have to hit "cntrl + c" to exit out of executing a payload or something.
3. You had better know Burp Suite and Wfuzz like the back of your dang hand! Also some others.
!!! BURP SUITE !!! - https://portswigger.net/burp/communitydownload
!!! WFUZZ !!! - https://wfuzz.readthedocs.io/en/latest/
!!! HAKRAWLER !!! - https://github.com/hakluke/hakrawler
!!! CRACKMAPEXEC !!! - https://github.com/byt3bl33d3r/CrackMapExec
!!! IMPACKET !!! - https://github.com/fortra/impacket
!!! BLOODHOUND !!! - https://github.com/BloodHoundAD/BloodHound
!!! EVIL-WINRM !!! - https://github.com/Hackplayers/evil-winrm
!!! EVIL-SSDP !!! - https://github.com/initstring/evil-ssdp
...I'll add more if I can think of any others later.
=========================================================================================
Here's 49 of the 400 machines you can do alongside me!
:D
https://www.youtube.com/watch?v=NQ6jbKqkJ0s&list=PLJrSyRNlZ2EeqkJa12Tu-Ezun9kXvHufN
=========================================================================================
PT 3.
FULLY AND COMPLETELY UNDERSTAND AND HAVE WORKED WITH THE FOLLOWING (You got this.):
1. Bash, python, C/C++, C#, perl, PHP, ASP, Javascript, Java, SAS, LATEX (at least know how to move code around for exploits to work)
2. TCP/IP PROTOCOLS TO KNOW FULLY or at least like 80-95%:
Protocol, Port Number:
FTP, 20/21
SSH, 22
Telnet, 23
SMTP, 25
DNS, 53
DHCP, 67/68
TFTP, 69
HTTP, 80-8000-8080-443,8443,10443
WEBMIN PORTS: 10,000s (look out for those high ports where things hide)
POP3, 110
NTP, 123
IMAP, 143
SNMP, 161/162
IRC, 194 6667
LDAP, 389
HTTPS, 443
SMB, 445
SMTPS, 465
IMAPS, 993
POP3S, 995
RDP, 3389
MSSQL, 1433
MySQL, 3306
PostgreSQL, 5432
VNC, 5900
MongoDB, 27017
Redis, 6379
RIP, 520
Kerberos, 88
MSRPC, 135
NetBIOS, 139
AFP (Apple Filing Protocol), 548
SIP (Session Initiation Protocol), 5060/5061
NNTP (Network News Transfer Protocol), 119
LDAP (over SSL), 636
FTP (over TLS/SSL), 990
Telnet (over SSL), 992
IMAP4 (over SSL), 993
POP3 (over SSL), 995
RADIUS, 1812/1813
IKE (Internet Key Exchange), 500
3. Use Seclists. Always.
$ apt-get install -y seclists
OR
$ cd /opt/
$ git clone https://github.com/danielmiessler/SecLists.git
raft-medium-files
raft-medium-words
raft-medium-directories
0-999 digits
various XSS wordlists (though you should know this by heart and manually)
various SQLi wordlists (though you should know this by heart and manually)
various Command Injection wordlists (though you should know this by heart and manually)
4. Reporting & CVSS Scoring:
Finding Title: <title of finding>
Severity: (Info, Low, Moderate, High, Critical)
CVSS Score:
* CIA TRIAD - https://www.geeksforgeeks.org/the-cia-triad-in-cryptography/
* SCORE CALCULATOR --> https://www.first.org/cvss/calculator/3.0
Endpoint(s), IP(s):
Description:
<formal description including an impact statement>
Evidence:
<screenshot evidence of key screen-space - remember to REDACT or BLUR credentials - even for formal reports>
Remediation & Mitigation Strategies:
<One Paragraph can be provided here or, depending on the org - at the bottom of the Formal Report.>
CWE: <title>
<CWE LINK>
* Additional Resource 1
* Additional Resource 2
* Additional Resource 3
=========================================================================================
=========================================================================================
PT 3.
1. You wanna be an Intruder?
Think like one.
2. A White Hat is earned. Remember that
=========================================================================================
=========================================================================================
PT4.
OSCP PREP VULNERABLE MACHINES:
1. https://rana-khalil.gitbook.io/hack-the-box-oscp-preparation/
2. "S1REN, what machine's should I work at? In order?"
My buddy TJ has you covered there 8-)
https://docs.google.com/spreadsheets/u/1/d/1dwSMIAPIam0PuRBkCiDI88pU3yzrqqHkDtBngUHNCw8/htmlview?pli=1
3. DO THOSE AND THEN LIKE 300 MORE.
=========================================================================================
=========================================================================================
PT 5. Binexp (Binary Exploitation)
Go for your OSED after OSCP/OSWA if you want to - however, AT LEAST UNDERSTAND A STACK BASED BUFFER OVERFLOW. Some of the payloads you work with are going to require you to work with "shellcode", "padding", or even "offsets" among other gadgets and things in order to get you that $--- Bling Bling ---$.
A stack-based buffer overflow is excellent to teach you this stuff.
Anything beyond that is not "as" necessary these days.
Most payloads are local.. at least at the time of writing this.
Vuln server.
https://thegreycorner.com/vulnserver.html
Immunity Debugger.
https://debugger.immunityinc.com/ID_register.py - put in some bogus info or whatever
Mona.py - this is your friend.
https://github.com/corelan/mona
Binary Ninja - this is your friend.
Tired of having to go through ASM? Here it is as plain-text code 👌:
https://binary.ninja/
Walkthrough to start with:
https://infosecwriteups.com/stack-based-buffer-overflow-practical-for-windows-vulnserver-8d2be7321af5
"Blessed the Angels above, we control EIP"
-Muts
=========================================================================================
=========================================================================================
PT 6.
Know how to speak professionally in interviews, in-person, and with executives.
This means back straight, TALK with a smile and project confidence. Afterall - look at what you've been through to get to this point.
400+ machines.
Sheesh… serious though.
Localize it all also. :)
=========================================================================================
=========================================================================================
PT 7.
Host Discovery Scan:
$ nmap -p 20,21,22,23,25,53,67,68,69,80,110,123,143,161,162,194,389,443,445,465,993,995,3389,1433,3306,5432,5900,27017,6379,520,88,135,139,548,5060,5061,119,636,990,992,993,995,1812,1813,500 -iL <in-scope file>
2. My preferred scans
$ export IP="x.x.x.x"
$ nmap -p- -sV -sT -A $IP --open
^ That's a big TCP connect and small vulnerability scan.
^ ^ We add --open because we don't want to waste tons of time scanning CLOSED ports….only open ones.
(depends if stateful or stateless firewall...)
$ nmap -p- -sC $IP --open
# Simple scripts only. All TCP Ports.
$ nmap -p- --script=vuln $IP
# Vuln scan. Takes forever - super noisy - but there you go.
$ nmap -sn 192.168.1.0-254
# Class-C 192 Private IP-address space Host Discovery
# thinc.local.....
=========================================================================================
=========================================================================================
====MASTER NOTE TEMPLATE...this is my main methodology for-each machine.
[OS]:
[Web-Technology]:
[Hostname]:
[IP]:
[USERS]:
[CREDENTIALS]:
=========================================================================
[To-Try LIST]:
=========================================================================
[NMAP RESULTS]:
=========================================================================
[Web Services Enumeration]:
=========================================================================
[OTHER / PRIVILEGE-ESCALATION]:
=========================================================================
Take Away Concepts (for the flat-file reference system):
*
*
*
<take away footholds/commands/hacks/etc>
(STORE THEM LOCALLY so you can quickly call them off of the command-line land mine!)
=========================================================================================
Good luck, look up at the stars, you are one in a million loved and you are different.
Happy hacking, Intruder.

Comments are closed.